managed detection and response providers: Top 10 Best 2025
The Growing Need for Expert Threat Detection
Let’s face it – the cybersecurity world has gotten scary. In 2023 alone, organizations faced an average of 1,876 attacks per week. That’s not a typo – nearly 2,000 attempts to breach your systems every single week. And as threat actors get more sophisticated (hello, AI-powered attacks), the gap between available talent and security needs keeps widening.
I’m Ryan Carter, founder and CEO of NetSharx Technology Partners. Over the years, I’ve watched dozens of businesses struggle with this exact problem. The good news? I’ve helped these same organizations slash cybersecurity costs while improving their threat response times by 40% through strategic partnerships with managed detection and response providers.
For most businesses, building your own 24/7 Security Operations Center just isn’t realistic – neither from a budget perspective nor a talent one. With 60% of organizations facing moderate to extreme risk due to security talent shortages, there’s a clear need for expert help.
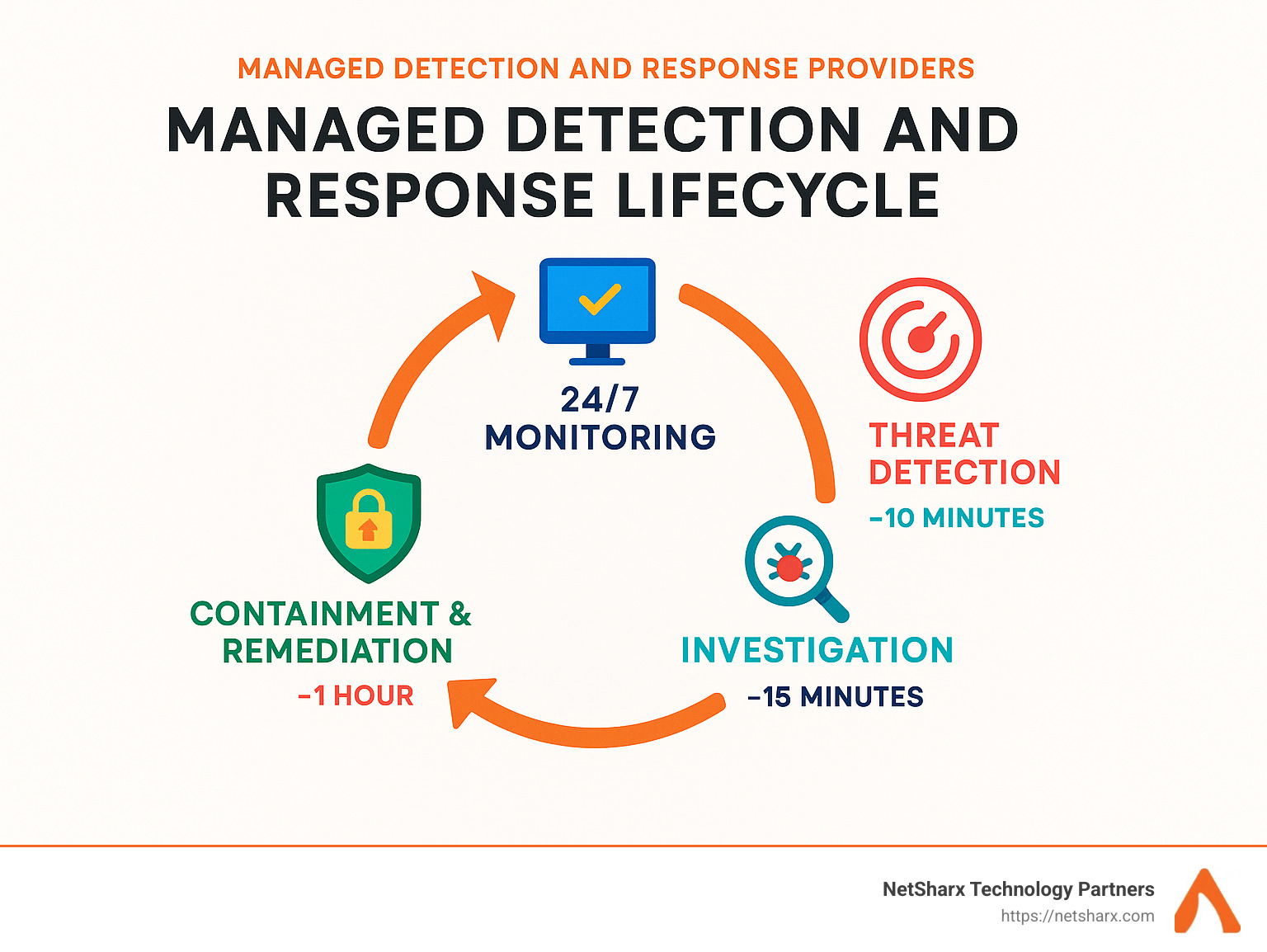
This is precisely where managed detection and response providers deliver tremendous value. They offer enterprise-grade security capabilities without the massive overhead of maintaining an in-house team. These specialized services provide round-the-clock monitoring, advanced threat detection, and rapid incident response for organizations that lack internal resources.
If you’re currently evaluating MDR solutions, here’s a quick snapshot of top providers based on industry reviews:
| Provider | Rating | Key Strength |
|---|---|---|
| Provider A | 4.8/5 | Serves 17,000+ customers worldwide |
| Provider B | 4.8/5 | Pioneer in concierge security model |
| Provider C | 4.7/5 | 95% reviewer recommendation rate |
| Provider D | 4.6/5 | Complete platform integration |
| Provider E | 4.5/5 | 69% cyber risk profile reduction |
Want to dive deeper into how these services can protect your business? We’ve got you covered with these resources:
- benefits of managed detection and response
- cloud security managed services
- how does managed detection and response work
Understanding Managed Detection and Response Providers
The cybersecurity world is buzzing about MDR services, and for good reason. Gartner predicts that by 2025, half of all organizations will be using managed detection and response providers – a dramatic jump from today’s adoption rates. This surge isn’t surprising when you consider the perfect storm of increasingly sophisticated threats and the persistent shortage of qualified security professionals.
But what exactly are managed detection and response providers? Think of them as your organization’s security guardians, delivering remotely managed Security Operations Center (SOC) functions that don’t just monitor your systems – they actively hunt for threats and step in when trouble appears. Unlike traditional security monitoring services that might simply alert you to problems, MDR combines powerful technology with human expertise to detect, analyze, and respond to threats.
According to data reported by Gartner, the most effective MDR services offer a comprehensive approach that includes round-the-clock monitoring, human-led threat hunting, careful incident validation to reduce false alarms, and either guided or fully managed incident response. Many also provide recommendations to strengthen your overall security posture based on what they’re seeing in your environment.
“MDR is conceptually related to both incident response software and endpoint detection and response software but solves the same issues in the form of a managed service,” notes Gartner in their market definition. It’s like having an elite security team on call without the overhead of building one yourself.
Why Organizations Choose Managed Detection and Response Providers
The cybersecurity skills gap isn’t just a talking point – it’s a genuine crisis affecting organizations worldwide. With 60% of companies reporting moderate to extreme risk due to security talent shortages, many are turning to managed detection and response providers as their lifeline.
Expertise on demand is perhaps the most compelling reason. Rather than spending months recruiting, hiring, and training security specialists (if you can find them at all), MDR delivers immediate access to seasoned professionals. As one CISO put it, “An MDR can work alongside an internal team, becoming a trusted partner who speaks our language and allows us to focus on securing our infrastructure instead of chasing after the small stuff.”
The cost efficiency is undeniable too. Building a 24/7 SOC in-house requires significant investment in technology, personnel, and ongoing training. MDR services offer enterprise-grade security at a predictable monthly cost. The numbers speak for themselves – industry research found that MDR customers realized a 254% ROI over three years.
When threats emerge, faster response times can make all the difference. Leading MDR services dramatically reduce the time between detection and resolution. Industry reports show impressive 20-minute mean time to respond on high/critical incidents, while one customer shared that they beat their mean time to remediate by more than 60%.
For regulated industries, compliance support is invaluable. MDR services help organizations meet requirements by providing the continuous monitoring, incident response capabilities, and documentation needed for frameworks like HIPAA, PCI DSS, and GDPR.
Perhaps most importantly, MDR services deliver measurable risk reduction. Leading MDR customers reported a 69% reduction in their cyber risk profile after implementation – a compelling testament to the value of expert-led detection and response.
Core Features Offered by Managed Detection and Response Providers
The best managed detection and response providers deliver a comprehensive set of capabilities designed to detect and neutralize threats across your entire digital footprint. They start with multi-source telemetry collection, gathering data from endpoints, networks, cloud environments, email systems, and identity providers to create a complete picture of your security landscape.
Their advanced detection capabilities go far beyond simple signature matching. Leading providers leverage behavioral analytics, machine learning, and threat intelligence to identify suspicious activity. Top MDR providers employ over 4,000 behavioral analytics mapped to the MITRE ATT&CK framework for comprehensive coverage.
What truly sets MDR apart is expert-led threat hunting. While automated systems catch many threats, human analysts proactively search for the ones that might slip through. As industry analysts have noted: “If the cybersecurity industry needs one example of how to make threat intelligence useful and drive detection engineering efforts via threat hunting, look no further.”
When incidents occur, thorough investigation and context help you understand what happened. MDR analysts provide detailed analysis including root cause determination and impact assessment. Advanced MDR technology visually maps attack paths from origin to closure, making investigations faster and more intuitive.
Depending on your service level, providers offer either guided or automated response – either walking your team through remediation steps or directly intervening to contain and eliminate threats. Some providers even offer automated rollback capabilities to restore systems to their pre-attack state.
Finally, ongoing security posture improvement recommendations help strengthen your defenses based on observed threats and vulnerabilities. As one customer noted, “We work arm-in-arm with our MDR provider to constantly tune our environment to improve our readiness both for what we can see, and what threat actors have yet to release.”
MDR vs. MSSP, SIEM, EDR & XDR
Navigating the alphabet soup of cybersecurity solutions can be overwhelming. As someone who’s guided dozens of confused clients through this maze, I want to help you understand how managed detection and response providers fit into the bigger picture.
Think of MDR as your dedicated security team that not only spots threats but actively fights them off – while other solutions might just sound the alarm and leave you to figure out what to do next. Let’s break down these differences in practical terms:
| Aspect | MDR | MSSP | SIEM | EDR | XDR |
|---|---|---|---|---|---|
| Primary function | 24/7 threat detection, investigation & response | Broad security management & monitoring | Log collection & correlation | Endpoint visibility & response | Cross-domain detection & response |
| Human element | Security analysts & threat hunters | Varies (often alert-focused) | Minimal (tool-focused) | Minimal (tool-focused) | Varies by implementation |
| Response capabilities | Active threat containment & remediation | Often limited to alerting | Alert generation | Endpoint containment | Cross-domain containment |
| Threat hunting | Core service component | Typically an add-on | Not included | Limited to endpoints | Varies by implementation |
| Technology ownership | Provider-managed stack | Customer or provider tools | Customer-owned | Customer-owned | Customer-owned |
| Pricing model | Subscription (often per-endpoint or user) | Tiered services | Software licensing + implementation | Software licensing | Software licensing |
MDR vs. MSSP (Managed Security Service Provider)
I like to explain this difference with a simple analogy: An MSSP is like a home security system that calls to tell you someone broke a window, while managed detection and response providers are more like having security guards who not only alert you but also chase down the intruder and secure your home.
Traditional MSSPs typically manage your security devices and send alerts when something looks fishy. They’re great for basic security monitoring, but they often leave the heavy lifting to you. As one of our clients, an IT director at a manufacturing firm, put it: “MSSPs tell you something happened; MDR tells you what happened, why it matters, and what to do about it.”
MDR vs. SIEM (Security Information and Event Management)
SIEM platforms are powerful tools that collect and analyze security logs from across your organization. But here’s the catch – they’re just tools. Without skilled professionals to operate them, they’re like having a high-end kitchen without a chef.
Managed detection and response providers incorporate SIEM capabilities but add the secret sauce – human expertise. Their analysts investigate alerts, weed out false positives, and coordinate response activities. As ReliaQuest aptly puts it, “SIEM is a technology; MDR is a service that may leverage SIEM as part of its technology stack.”
MDR vs. EDR (Endpoint Detection and Response)
EDR solutions are laser-focused on protecting your endpoints – the laptops, desktops, and servers where most work happens. They provide excellent visibility but have two limitations: they only see endpoints (not networks or cloud), and they still need someone to manage them effectively.
MDR services often build on EDR technology but extend protection across your entire environment while adding human-led investigation and response. It’s like upgrading from a security camera on your front door to a comprehensive system covering your entire property, plus hiring someone to monitor it 24/7.
MDR vs. XDR (Extended Detection and Response)
XDR platforms represent the evolution of EDR, extending visibility across multiple security domains. They integrate data from endpoints, networks, cloud workloads, and applications to provide a more complete picture. However, like other technologies, XDR still requires skilled operators.
Many managed detection and response providers are now offering MXDR (Managed XDR), combining XDR platforms with human expertise. This gives you the best of both worlds – comprehensive visibility and active response from security professionals who know how to interpret the data and take appropriate action.
The bottom line? While technologies like SIEM, EDR, and XDR are powerful tools, managed detection and response providers offer something they can’t – the human element of security expertise working around the clock to protect your business.
Evaluation Criteria: Picking the Right Partner
Finding your perfect managed detection and response provider match doesn’t have to feel overwhelming. At NetSharx Technology Partners, we’ve helped dozens of organizations steer these waters, and we’ve developed a straightforward framework that cuts through the complexity.
Think of choosing an MDR provider like finding a good business partner – you need someone who understands your specific needs, works well with your existing setup, and delivers real value for your investment.
Use Case Alignment matters tremendously. Every organization faces different security challenges. Some worry most about ransomware, others about compliance requirements, and some about protecting sensitive intellectual property. I recently worked with a healthcare client who needed specialized protection for their patient data systems, while a manufacturing client prioritized security for their operational technology. Be clear about your security priorities when evaluating providers.
Technology Compatibility can make or break your MDR experience. Some providers require you to adopt their entire technology stack, which might mean replacing systems you’ve already invested in. Others can work with your existing tools. As one of our CISO clients put it, “We needed an MDR that could leverage our existing Microsoft security investments rather than forcing us to rip and replace.” Always ask about integration capabilities upfront.
The Coverage Breadth of an MDR service tells you what they’re actually watching. The best managed detection and response providers keep an eye on your entire digital footprint – from laptops and servers to network traffic, cloud environments, business applications, and even email systems. Gaps in coverage can leave dangerous blind spots where threats can hide.
When it comes to Response Capabilities, there’s a world of difference between providers. Some will simply notify you about threats and offer advice, while others will actively jump in to contain and eliminate the threat. Consider what you need – if your internal team is small or lacks specialized security expertise, you’ll want a provider that offers hands-on response with clear SLAs for how quickly they’ll act.
Understanding the Pricing Model and Scalability helps avoid budget surprises down the road. Most providers charge per endpoint or per user, but some offer tiered pricing based on organization size. I always recommend clients ask about what happens as they grow – will costs scale linearly or are there volume discounts? Also check if specialized services like threat hunting are included or cost extra.
Good Reporting and Metrics transform security data into actionable insights. Look for providers that offer both executive-level summaries (perfect for board updates) and detailed technical reports for your security team. The best reports clearly show what threats were detected, how they were handled, and what security improvements are recommended.
Threat Hunting Inclusion is a key differentiator that separates basic alert monitoring from true threat detection. While automated systems catch known threats, human-led hunting finds the sneaky attackers who evade standard defenses. Some MDR providers include regular threat hunting in their base service, while others charge extra – be sure to clarify this point.
Clear Service Level Agreements set proper expectations for both parties. They should specify how quickly the provider will triage alerts, respond to incidents, and communicate with you during a security event. Without defined SLAs, you might find yourself waiting for critical responses during an active incident.
The Security Expertise and Staffing behind an MDR service makes all the difference. Ask about the qualifications of the security analysts who’ll be monitoring your environment, where their SOC is located, and how many clients each analyst handles. A provider with overworked analysts managing too many clients can’t deliver the attention your security deserves.
Finally, some forward-thinking managed detection and response providers now offer Risk Transfer Options like warranties or insurance. For example, Arctic Wolf provides a Security Operations Warranty with financial protection up to $1.5 million if a breach occurs despite their protection. These options can provide additional peace of mind for organizations concerned about financial impacts from security incidents.
At NetSharx Technology Partners, we remain vendor-neutral to help you find the MDR provider that truly matches your specific needs – not just the one with the biggest marketing budget or the most recognizable name. Our goal is finding the right security fit for your unique situation, technology environment, and budget reality.
The Managed Detection and Response Providers Landscape
The MDR market is experiencing rapid growth and evolution. According to Gartner, 40% of midsize enterprises will be using MDR as their only managed security service by 2024, while 50% of organizations overall will adopt MDR services by 2025.
The landscape of managed detection and response providers is diverse, ranging from established cybersecurity vendors expanding into MDR to specialized providers focused exclusively on detection and response services. The market includes:
- Endpoint security vendors who have expanded their EDR platforms with managed services
- Traditional MSSPs that have evolved their offerings to include active response capabilities
- Pure-play MDR providers built specifically for detection and response
- Consulting firms that have developed MDR capabilities
- Telecommunications companies offering MDR as part of broader security portfolios
This diversity creates both opportunities and challenges for organizations seeking the right partner. At NetSharx Technology Partners, we maintain relationships with a wide range of providers to ensure we can match our clients with the MDR service that best fits their specific needs.
Measuring Success with Managed Detection and Response Providers
Effective managed detection and response providers deliver measurable security improvements that justify their cost. Key performance indicators (KPIs) to track include:
1. Mean Time to Detect (MTTD)
How quickly threats are identified after initial compromise. Leading MDR providers can reduce MTTD from the industry average of 207 days to hours or minutes.
2. Mean Time to Respond (MTTR)
The elapsed time between detection and containment. Top providers report MTTR metrics ranging from 6 minutes to 22 minutes for critical threats.
3. Dwell Time Reduction
The total time attackers remain undetected in the environment. Effective MDR services dramatically reduce this metric, limiting potential damage.
4. False Positive Rate
The proportion of alerts that turn out to be benign. Quality MDR services apply human analysis to dramatically reduce false positives—some providers report just 0.1 false positives per day.
5. Threat Detection Efficacy
The percentage of real threats successfully identified. Leading MDR providers report 99% threat accuracy in their detections.
6. Return on Investment (ROI)
The financial benefits relative to costs. MDR customers report a 610% ROI over three years, according to third-party analysis.
7. Security Posture Improvement
Measurable improvement in overall security readiness. MDR customers report a 69% reduction in their cyber risk profile.
8. Operational Impact
Time savings for internal security teams. 64% of MDR customers report more time to focus on other security initiatives, while 60% report more time for professional development.
Endpoint-Centric Specialists
When it comes to protecting your most vulnerable assets, endpoint-centric managed detection and response providers shine brightest. These specialists focus their expertise on safeguarding the devices that your team uses every day—laptops, desktops, servers, and mobile devices—which are often the first targets in a cyberattack.
Think of these providers as having a laser focus on the places where your employees actually work. They build their services around robust EDR (Endpoint Detection and Response) platforms that give them incredibly detailed visibility into what’s happening on each device.
Comprehensive endpoint visibility is the foundation of what makes these providers effective. They deploy lightweight agents across your organization’s devices that continuously monitor processes running in the background, changes to important files, modifications to the system registry, network connections, and user activities. This deep visibility helps catch sophisticated attacks that might slip past traditional antivirus solutions.
Rather than just looking for known malware signatures, the best endpoint MDR teams use behavioral analysis and machine learning to spot suspicious patterns. Leading providers leverage artificial intelligence to detect unusual activities that might indicate a threat—even if that specific threat has never been seen before. It’s like having a security guard who doesn’t just check faces against a “known criminals” list but also notices when someone is acting suspiciously.
When threats are detected, rapid containment capabilities become crucial. Endpoint-focused managed detection and response providers can quickly isolate affected systems to prevent attackers from moving laterally through your network. This containment ability is particularly important for stopping fast-spreading threats like ransomware before they can encrypt all your data.
One of the most impressive capabilities some providers offer is rollback and remediation. Imagine being able to turn back time on an infected system, automatically restoring it to how it was before the attack happened. As one customer put it, “Previously, some attacks had evaded our detection. Our MDR provider investigated the roots and weeded out those threats.” This capability can dramatically reduce downtime and recovery costs after an incident.
The forensic investigation capabilities of endpoint-focused MDR teams provide valuable context about attacks. They can tell you exactly how attackers got in, which systems were affected, and whether any sensitive data was exposed. This detailed understanding isn’t just helpful for cleaning up after an attack—it’s essential for patching the vulnerabilities that allowed the attack to happen in the first place.
Many endpoint-centric providers also incorporate user behavior analytics to detect insider threats or compromised accounts. By establishing baselines of normal behavior for each user, these systems can spot when someone starts accessing unusual files or connecting to systems they normally don’t use—potentially indicating that their account has been compromised or that they’re up to something they shouldn’t be.
For organizations particularly concerned about ransomware defense, endpoint-focused MDR services offer specialized capabilities like detecting encryption activities, monitoring for known ransomware behaviors, and implementing immediate isolation protocols when ransomware is suspected. Some can even detect the early signs of a ransomware attack days or weeks before the actual encryption begins, during the initial access and reconnaissance phases.
At NetSharx Technology Partners, we’ve seen how the right endpoint-centric MDR provider can transform an organization’s security posture, often serving as the foundation for a broader security strategy that can be expanded over time.
Network & Log Analytics Hubs
Network and log-focused managed detection and response providers bring a different approach to cybersecurity by focusing on what’s happening across your network rather than just on individual devices. These specialists excel at spotting threats that reveal themselves through network behavior patterns or leave breadcrumbs in your system logs.
Think of these providers as digital detectives who monitor the highways and byways of your network, watching for suspicious travelers and unusual activity. Their strength lies in their ability to see the big picture of your environment.
Network Traffic Analysis forms the backbone of these services. By examining how data moves around your network, these providers can spot the telltale signs of an attack in progress. They can identify when attackers try to communicate with command-and-control servers, attempt to steal data, or move sideways through your network hunting for valuable assets. Some deploy specialized sensors that look deep into packet contents, while others focus on analyzing metadata patterns.
“The network doesn’t lie,” as one security analyst put it. “When attackers are active, they leave footprints in network traffic that endpoint security might miss.”
Log Collection and Correlation is another crucial capability these providers offer. By gathering logs from your firewalls, servers, cloud services, and applications, they create a comprehensive view of activity across your environment. Their correlation engines can connect dots between seemingly unrelated events, revealing attack patterns that might otherwise go unnoticed. This approach proves particularly effective at catching sophisticated attacks that unfold across multiple systems or over extended timeframes.
Many of these managed detection and response providers also incorporate User and Entity Behavior Analytics (UEBA) into their services. This technology establishes baseline patterns of normal behavior for users and systems, then flags deviations that might indicate compromise. Unusual login times, unexpected access to sensitive resources, or strange data transfer patterns all trigger alerts for human analysts to investigate.
When threats are detected, these providers can implement Network-Based Containment measures to stop attacks in their tracks. This might include blocking communication with malicious IP addresses, isolating affected network segments, or implementing firewall rules to cut off command-and-control communications. Their ability to respond at the network level provides a critical layer of defense when endpoint protections fail.
The best network and log analytics hubs also integrate extensive Threat Intelligence into their detection capabilities. By incorporating the latest information about known threats, they can quickly identify when attackers are using infrastructure or techniques associated with specific threat actors. This real-time intelligence dramatically improves detection rates for both known and emerging threats.
At NetSharx Technology Partners, we’ve seen organizations significantly strengthen their security posture by partnering with network-focused MDR providers, especially when combined with endpoint protection. This layered approach ensures threats have fewer places to hide and provides comprehensive visibility across the entire attack surface.
Cloud-Native MDR Platforms
As organizations accelerate their cloud adoption, cloud-native managed detection and response providers have emerged to address the unique security challenges of cloud environments. These providers specialize in protecting infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS), and software-as-a-service (SaaS) resources.
Key capabilities of cloud-native MDR providers include:
1. Multi-Cloud Coverage
Leading providers offer comprehensive protection across major cloud platforms including AWS, Microsoft Azure, and Google Cloud. This multi-cloud approach is essential for organizations with diverse cloud footprints.
2. API-Based Monitoring
Rather than deploying agents, cloud-native MDR services often leverage cloud provider APIs to monitor activities, configurations, and access patterns. This approach enables comprehensive visibility without performance impact.
3. Cloud Configuration Analysis
These providers continuously assess cloud configurations against security best practices and compliance requirements, identifying misconfigurations that could lead to breaches. For example, they might detect overly permissive storage buckets or inadequate encryption settings.
4. Identity and Access Monitoring
Cloud security heavily depends on identity controls. Cloud-native MDR services monitor authentication patterns, permission changes, and privilege usage to detect potential account compromises or insider threats.
5. Kubernetes and Container Security
For organizations using containerized applications, specialized MDR providers offer visibility into Kubernetes clusters, container images, and orchestration activities to identify vulnerabilities and suspicious behaviors.
6. DevOps Integration
Cloud-native MDR services often integrate with CI/CD pipelines and infrastructure-as-code tools to identify security issues early in the development process, enabling a shift-left security approach.
As one customer explained, “SentinelOne has changed the way we look at cloud security. It notified us in real time of what we missed. Previously, some attacks had evaded our detection.”
Full-Stack Threat Hunters
The most sophisticated managed detection and response providers don’t just wait for alerts to come in – they actively hunt for threats lurking in your environment. These elite providers combine powerful technology with expert human analysts who proactively search for signs of compromise across your entire IT landscape.
Think of these threat hunters as digital detectives, constantly investigating your systems for evidence that others might miss. They bring a human element that automation alone simply cannot match.
The Human Touch in a Digital World
What makes full-stack threat hunters truly special is their hypothesis-driven approach. Rather than simply responding to what technology flags, they conduct structured hunting missions based on the latest threat intelligence.
For example, if they notice a new technique being used by ransomware groups, they’ll proactively search your environment for any signs of those specific behaviors – often finding threats before they trigger any alerts. As one CISO from a Fortune 500 manufacturing corporation noted about their MDR provider:
“Our MDR provider brought to life a lot of activity in our environment that we were previously blissfully ignorant of — it was like flipping the lights on and watching the cockroaches scramble.”
Methodical and Comprehensive Coverage
The best hunting teams align their activities with the MITRE ATT&CK framework, ensuring they’re covering the full spectrum of known adversary tactics, techniques, and procedures (TTPs). This methodical approach means fewer blind spots in your security posture.
Leading MDR providers stand out in this area, with industry analysts noting they excel at “making threat intelligence useful and driving detection engineering efforts via threat hunting.” This practical application of threat intelligence is what separates true hunters from basic monitoring services.
Many providers also incorporate purple team exercises – blending offensive (red team) and defensive (blue team) tactics to simulate real-world attacks. This approach helps identify security gaps that might otherwise go unnoticed until an actual breach occurs.
Beyond Detection to Understanding
When full-stack hunters find something suspicious, they don’t just alert you and move on. They conduct in-depth forensic analysis to determine exactly what happened. This includes identifying affected systems, assessing potential data exposure, and uncovering any persistence mechanisms attackers may have established.
This thorough approach gives you a complete picture of the threat – not just that something happened, but how it happened, why it happened, and what you can do to prevent it from happening again.
Strategic Partners, Not Just Alert Generators
Perhaps most valuable is the strategic guidance these providers offer. Based on what they observe in your environment and the broader threat landscape, they provide actionable recommendations to strengthen your security posture.
For instance, if they notice attackers frequently exploiting a particular vulnerability in your environment, they won’t just help you fix those specific instances – they’ll recommend architectural changes to eliminate the entire class of vulnerability.
This forward-thinking approach transforms these managed detection and response providers from tactical response teams into strategic security partners who help you stay ahead of emerging threats.
At NetSharx Technology Partners, we’ve seen how the right full-stack threat hunting service can dramatically improve our clients’ security posture, often uncovering risks they never knew existed. The peace of mind that comes with knowing expert hunters are constantly watching your environment is invaluable in today’s threat landscape.
AI-Driven Autonomous Guards
Emerging managed detection and response providers are leveraging artificial intelligence and machine learning to deliver increasingly autonomous security capabilities. These providers combine human expertise with advanced algorithms to accelerate detection and response.
Key capabilities of AI-driven MDR providers include:
1. Machine Learning Detection Models
These providers train ML models on vast datasets of normal and malicious behaviors to identify subtle indicators of compromise. Leading providers analyze over 1,700 signals to detect anomalies that might be missed by traditional approaches.
2. Automated Alert Triage
AI systems automatically analyze and prioritize alerts based on severity, confidence, and potential impact, ensuring that human analysts focus on the most critical threats. Advanced MDR providers use AI-driven automation to prioritize, correlate, and enrich alerts in real time.
3. Anomaly Scoring and Prioritization
By establishing behavioral baselines for users, systems, and networks, these providers can assign anomaly scores to unusual activities, helping to identify the most significant deviations that warrant investigation.
4. Automated Containment
When high-confidence threats are detected, AI-driven MDR services can initiate automated containment actions such as isolating endpoints, blocking network connections, or revoking user access to limit damage.
5. Predictive Analytics
The most advanced providers use predictive models to identify systems at risk of compromise based on vulnerabilities, configurations, and exposure to known threats, enabling proactive hardening before attacks occur.
6. Continuous Learning and Improvement
These MDR services continuously refine their detection models based on new threat data, false positive feedback, and evolving attack techniques, ensuring that protection improves over time.
As one customer noted, “Our MDR provider allows us to target and resolve issues before they can take out our IT infrastructure, with automated tools and expert human advisors that point us in the right direction.”
Frequently Asked Questions about Managed Detection and Response
What’s the difference between MDR and XDR?
If you’re exploring cybersecurity solutions, you’ve likely encountered both MDR and XDR – similar acronyms that represent different approaches to security.
Managed Detection and Response (MDR) is essentially a complete security service delivered by real human experts who monitor your systems around the clock. Think of MDR as having a team of security professionals constantly watching your digital environment, investigating suspicious activities, and stepping in to handle threats when they appear. It’s like having an elite security team without the hassle of building one yourself.
Extended Detection and Response (XDR) is more of a technology platform – a sophisticated tool that pulls security data from multiple sources across your organization. XDR connects the dots between your endpoints, network, cloud services, and email systems to give you comprehensive visibility. However, XDR is primarily a tool that still requires skilled security professionals to operate effectively.
The lines between these solutions are increasingly blurring. Many managed detection and response providers now offer what they call MXDR (Managed XDR) – essentially combining the comprehensive visibility of XDR technology with the human expertise of MDR services. This gives you the best of both worlds: powerful technology backed by security experts who know how to use it.
How much does an MDR service cost compared to an in-house SOC?
When considering security investments, cost is naturally a major factor. Most managed detection and response providers charge between $15-40 per endpoint per month, with variations based on service level and additional features like proactive threat hunting. For a mid-sized organization with 500 employees, this typically translates to about $90,000-240,000 annually.
Building your own in-house Security Operations Center (SOC) is a significantly larger investment:
- Security tools alone (SIEM, EDR, etc.) can cost $100,000-500,000+ upfront
- Personnel is the biggest expense – you’ll need at least 5-6 analysts for 24/7 coverage, costing $500,000-800,000 annually
- Ongoing training and certifications add another $25,000-50,000 each year
- Infrastructure and operational costs contribute an additional $50,000-100,000 annually
As one CISO we worked with put it: “Choosing an MDR provider over the alternative means significant cost savings. Instead of spending twice the amount and hiring SOC engineers at $100k each, we get the benefit of best-in-class technology while spending less than what it would cost to hire a single SOC professional.”
The numbers back this up. Industry analysis typically reports 50% annual cost savings compared to building an in-house SOC, and independent research found a remarkable 254% ROI for MDR services over three years.
Can MDR help bridge the cybersecurity skills gap?
Absolutely! This is actually one of the most compelling reasons organizations turn to managed detection and response providers. With 60% of organizations reporting moderate to extreme risk due to security talent shortages, MDR services offer a practical solution to this widespread challenge.
MDR services help bridge the skills gap in several important ways:
First, they provide immediate access to security expertise. Instead of spending months recruiting (and competing for) scarce security talent, you gain instant access to trained professionals who are ready to protect your environment from day one.
Many MDR providers also work collaboratively with your internal team, sharing knowledge and best practices that help develop your in-house capabilities over time. This collaborative approach creates a valuable learning opportunity for your staff.
By handling the 24/7 monitoring and alert triage, MDR services free up your internal security team to focus on strategic initiatives rather than being buried in alerts. In fact, 64% of MDR customers report having more time for other security projects, while 60% say their teams now have more time for professional development.
Perhaps most importantly, MDR analysts receive continuous training on the latest threats and techniques. This ensures their skills remain current without requiring you to invest in expensive training programs or certifications.
As one customer told us, “Our MDR provider takes the intelligence they see across their customers’ environments and applies it immediately to us. That visibility and context fuels our own threat hunting and speeds up our reaction.”
At NetSharx Technology Partners, we’ve seen how the right MDR partnership can transform an organization’s security posture while addressing the persistent challenge of finding and retaining qualified security talent.
Conclusion
The landscape of managed detection and response providers continues to evolve rapidly, with services becoming more sophisticated, specialized, and effective at combating modern cyber threats. As we’ve explored throughout this review, MDR services offer a compelling solution for organizations facing the dual challenges of increasing threat complexity and cybersecurity talent shortages.
The cybersecurity world isn’t getting any simpler, is it? That’s why MDR adoption is accelerating so quickly. With Gartner predicting that 50% of organizations will use MDR services by 2025, these solutions are becoming a mainstream component of security strategies rather than a niche offering.
While the cost savings compared to building an in-house SOC are certainly attractive, I’ve found that my clients value MDR for much more than just financial benefits. The true value lies in improved security outcomes—those faster detection times, quicker responses, measurably reduced risk profiles, and that invaluable visibility across increasingly complex environments.
One of the most interesting developments I’ve observed is the growing specialization among providers. The market now includes MDR services focusing on specific domains like endpoint security, network monitoring, or cloud environments. Others have developed deep expertise in particular industries such as healthcare, financial services, or manufacturing. This specialization enables more customized security approaches custom to your specific needs.
AI and automation are fundamentally changing MDR capabilities. Leading providers are leveraging artificial intelligence to accelerate detection, handle routine tasks automatically, and even predict emerging threats before they impact your operations. This technological evolution is making MDR services more effective and efficient than ever before.
That said, I can’t stress enough that human expertise remains essential to effective security. Despite all the technological advances, the most effective MDR services combine those advanced tools with skilled analysts who provide context, conduct proactive threat hunting, and guide strategic security improvements. Technology alone simply can’t replace the intuition and creativity of experienced security professionals.
At NetSharx Technology Partners, we understand that selecting the right managed detection and response provider is a critical decision that impacts your organization’s security posture, operational efficiency, and risk profile. As a technology broker with an extensive provider network, we’re uniquely positioned to help you steer this complex landscape.
Our approach emphasizes unbiased assessment of your specific security needs, technical environment, and budget constraints without favoring any particular provider. We leverage our relationships with leading MDR providers to facilitate side-by-side comparisons of capabilities, pricing, and service levels, making it easier for you to see the differences that matter most.
Our proven methodology accelerates the decision-making process, helping you achieve consensus and move forward with implementation without the analysis paralysis that often plagues security decisions. And we don’t disappear after the contract is signed—we remain engaged throughout the relationship, ensuring that your MDR service continues to meet your evolving security requirements.
The threat landscape will continue to evolve, with attackers developing new techniques and targeting emerging technologies. By partnering with the right managed detection and response provider, you can build cyber resilience that adapts to these changes while focusing your internal resources on core business initiatives.
To learn more about how NetSharx Technology Partners can help you select and implement the ideal MDR solution for your organization, contact our cybersecurity experts for a no-obligation consultation.